I'd like to pose the topic of integrating SoftEther VPN services with others on the same IP and port.
For example, many here would be familiar with how Apache' VHOST configurations use SNI to permit multiple HTTPS or HTTP domains to share the same physical IP address and port.
Consider a possible configuration:
* Apache Server runs a number of HTTPS (443) VHOST sections, all sharing the same public IP address
* Each VHOST serves a different domain, identified by a unique DNS name via SNI
* It is desired that SoftEtherVPN be offered as another of these
Objectives would be that no special compile of SoftEther VPN or Apache' be required, and thus the integration be performed by a combination of more or less "standard" existing options. These desires could be set aside if some other means was a part of the SoftEther VPN planning.
One method that comes to mind is to configure an additional Apache VHOSTs as an SSL Reverse Proxy. The Apache' server process is separate from the SoftEther VPN process and runs on a different physical host machine.
This integrates well, but requires some adaptation of the traditional SoftEther VPN configuration. Namely, that SoftEther VPN's SSL functions be offloaded to the Apache' VHOST, perhaps even to the point where SoftEther VPN sees the tunnel as unencrypted. This would have the side benefit of potentially increased encryption strength (not presently offered by SoftEther VPN) and enable employment of hardware assisted crypto solutions.
However, some ambiguities arise. For example - It's not entirely clear how the SSL Client Certificate issues would be handled in this instance. Ideally, SoftEther VPN would retain Client related duties.
I am curious if anyone on the development team (or elsewhere) foresaw this Integration issue in thought or fact, and come to any solutions or can offer comments.
Thank you.
se VPN Integration
-
mashuser
- Posts: 5
- Joined: Sat Jan 17, 2015 1:18 am
Re: se VPN Integration
I have a similar setup with my webserver's HTTPS, SSH and SE-VPN all behind port 443.
I use haproxy and don't put SSL termination at the reverse proxy.
I terminate my SSL at the each backend.
SSL for subdomains is handled by CloudFlare.
Apache is configured with Certs for its port 8443, Cloudflare's SSL set to Flexible.
haproxy acts as switch, on the other hand you may terminate SSL at haproxy if you use the same certs for your website and SE-VPN... i'm just too lazy to figure it out how to make it work.
This works on the assumption that your website would not be accessed using old web browsers (browsers that do not understand/do SNI) and you configure your DNS well.
Older browsers would return HTTP 403. Forbidden, they would see your SE-VPN server at whatever backend port you are using.
Snippet of my haproxy config:
with comments marked by //
# Setting timeouts
timeout connect 45s
timeout client 2m
timeout server 2m
retries 5
timeout http-request 2m # Slowloris protection
timeout tarpit 2m # tarpit hold time
timeout queue 2m
backlog 10000
frontend ft_http
bind :80
mode http
option httpclose
default_backend bk_http
acl to_http hdr(host) -i domain.xyc //redundant configuration with apache's virtual hosts
acl to_http hdr(host) -i subdomain4.domain.xyc //redundant configuration with apache's virtual hosts
acl to_http hdr((host) -i subdomain1.domain.xyc //redundant configuration with apache's virtual hosts
acl to_http hdr(host) -i subdomain2.domain.xyc //redundant configuration with apache's virtual hosts
acl trans hdr(host) -i subdomain3.domain.xyc //redundant configuration with apache's virtual hosts/proxy pass
use_backend bk_http if to_http
use_backend bk_trans if trans
frontend ft_https
bind :443
mode tcp
tcp-request inspect-delay 2s
tcp-request content accept if HTTP
acl to_ssh req_ssl_sni -i ssh.domain.xyc
acl to_ssh payload(0,7) -m bin 5353482d322e30
acl to_https req_ssl_sni -i domain.xyc
acl to_https req_ssl_sni -i subdomain1.domain.xyc
acl to_https req_ssl_sni -i subdomain2.domain.xyc
acl to_https req_ssl_sni -i subdomain4.domain.xyc
acl to_https req_ssl_sni -i subdomain3.domain.xyc
acl to_softether req_ssl_sni -i vpn.domain.xyc
acl to_softether req_ssl_sni -i secure.domain.xyc
acl to_softether req_ssl_sni -i domain.xyc/tcp
acl to_softether req_ssl_sni -i res.domain.xyc
acl to_softether req_ssl_sni -i res.domain.xyc/tcp
acl to_softether req_ssl_sni -i domainxyz.softether.net
acl to_softether req_ssl_sni -i domainxyz.v4.softether.net
acl to_softether req_ssl_sni -i domainxyz.softether.net/tcp
acl to_softether req_ssl_sni -i domainxyz.v4.softether.net/tcp
acl to_softether req_ssl_sni -i 198.51.100.23
acl to_openvpn req_ssl_sni -i 198.51.100.23 //doesnt work, used SE-VPN's openvpn clone server instead
acl to_openvpn req_ssl_sni -i ovpn.domain.xyc //doesnt work, used SE-VPN's openvpn clone server instead
use_backend bk_ssh if to_ssh
use_backend bk_softether if to_softether
use_backend bk_openvpn if to_openvpn
use_backend bk_https if to_https
default_backend bk_softether
backend bk_ssh
mode tcp
server ssh 127.0.0.1:22 //backend ssh server at normal port 22
timeout server 2h //timeout for 2 hours
option tcpka //keepalive
backend bk_softether
mode tcp
server softether 127.0.0.1:995 //port used by softether
backend bk_openvpn
mode tcp
server openvpn 127.0.0.1:1194 //port used by sni enabled openvpn, this doesnt work anyway
//doesnt work, used SE-VPN's openvpn clone server instead
backend bk_http
mode http
server apache 127.0.0.1:81 //backend webserver at port 81
backend bk_https
mode tcp
server apache 127.0.0.1:8443 //backend webserver at port 8443
backend bk_trans
mode http
server transmission 127.0.0.1:9091 //backend transmission webclient
I use haproxy and don't put SSL termination at the reverse proxy.
I terminate my SSL at the each backend.
SSL for subdomains is handled by CloudFlare.
Apache is configured with Certs for its port 8443, Cloudflare's SSL set to Flexible.
haproxy acts as switch, on the other hand you may terminate SSL at haproxy if you use the same certs for your website and SE-VPN... i'm just too lazy to figure it out how to make it work.
This works on the assumption that your website would not be accessed using old web browsers (browsers that do not understand/do SNI) and you configure your DNS well.
Older browsers would return HTTP 403. Forbidden, they would see your SE-VPN server at whatever backend port you are using.
Snippet of my haproxy config:
with comments marked by //
# Setting timeouts
timeout connect 45s
timeout client 2m
timeout server 2m
retries 5
timeout http-request 2m # Slowloris protection
timeout tarpit 2m # tarpit hold time
timeout queue 2m
backlog 10000
frontend ft_http
bind :80
mode http
option httpclose
default_backend bk_http
acl to_http hdr(host) -i domain.xyc //redundant configuration with apache's virtual hosts
acl to_http hdr(host) -i subdomain4.domain.xyc //redundant configuration with apache's virtual hosts
acl to_http hdr((host) -i subdomain1.domain.xyc //redundant configuration with apache's virtual hosts
acl to_http hdr(host) -i subdomain2.domain.xyc //redundant configuration with apache's virtual hosts
acl trans hdr(host) -i subdomain3.domain.xyc //redundant configuration with apache's virtual hosts/proxy pass
use_backend bk_http if to_http
use_backend bk_trans if trans
frontend ft_https
bind :443
mode tcp
tcp-request inspect-delay 2s
tcp-request content accept if HTTP
acl to_ssh req_ssl_sni -i ssh.domain.xyc
acl to_ssh payload(0,7) -m bin 5353482d322e30
acl to_https req_ssl_sni -i domain.xyc
acl to_https req_ssl_sni -i subdomain1.domain.xyc
acl to_https req_ssl_sni -i subdomain2.domain.xyc
acl to_https req_ssl_sni -i subdomain4.domain.xyc
acl to_https req_ssl_sni -i subdomain3.domain.xyc
acl to_softether req_ssl_sni -i vpn.domain.xyc
acl to_softether req_ssl_sni -i secure.domain.xyc
acl to_softether req_ssl_sni -i domain.xyc/tcp
acl to_softether req_ssl_sni -i res.domain.xyc
acl to_softether req_ssl_sni -i res.domain.xyc/tcp
acl to_softether req_ssl_sni -i domainxyz.softether.net
acl to_softether req_ssl_sni -i domainxyz.v4.softether.net
acl to_softether req_ssl_sni -i domainxyz.softether.net/tcp
acl to_softether req_ssl_sni -i domainxyz.v4.softether.net/tcp
acl to_softether req_ssl_sni -i 198.51.100.23
acl to_openvpn req_ssl_sni -i 198.51.100.23 //doesnt work, used SE-VPN's openvpn clone server instead
acl to_openvpn req_ssl_sni -i ovpn.domain.xyc //doesnt work, used SE-VPN's openvpn clone server instead
use_backend bk_ssh if to_ssh
use_backend bk_softether if to_softether
use_backend bk_openvpn if to_openvpn
use_backend bk_https if to_https
default_backend bk_softether
backend bk_ssh
mode tcp
server ssh 127.0.0.1:22 //backend ssh server at normal port 22
timeout server 2h //timeout for 2 hours
option tcpka //keepalive
backend bk_softether
mode tcp
server softether 127.0.0.1:995 //port used by softether
backend bk_openvpn
mode tcp
server openvpn 127.0.0.1:1194 //port used by sni enabled openvpn, this doesnt work anyway
//doesnt work, used SE-VPN's openvpn clone server instead
backend bk_http
mode http
server apache 127.0.0.1:81 //backend webserver at port 81
backend bk_https
mode tcp
server apache 127.0.0.1:8443 //backend webserver at port 8443
backend bk_trans
mode http
server transmission 127.0.0.1:9091 //backend transmission webclient
-
kh_tsang
- Posts: 551
- Joined: Wed Jul 24, 2013 12:09 pm
Re: se VPN Integration
If you use Cloudflare, that means the content is decrypted by Cloudflare and encrypted again. If you use Flexible SSL in Cloudflare, that means the web traffic between Cloudflare and the server is not encrypted. This breaks the end-to-end connectivity.
-
hans@dijkewijk.nl
- Posts: 1
- Joined: Wed Feb 14, 2024 12:34 pm
Re: se VPN Integration
This is an old item, but still relevant I think.
SoftEther VPN and HTTP/s on the same IPv4 address
It is not clear right away how to setup a SoftEther VPN over port 443 shared with a HTTPs server.
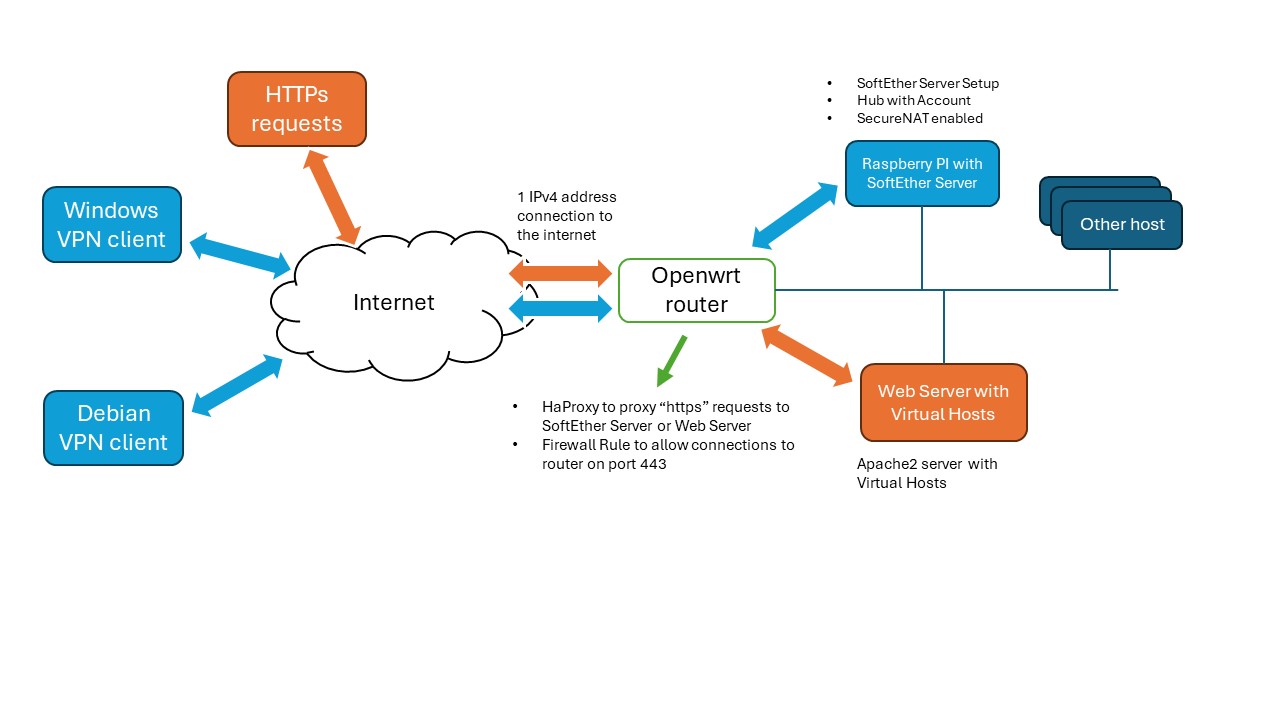
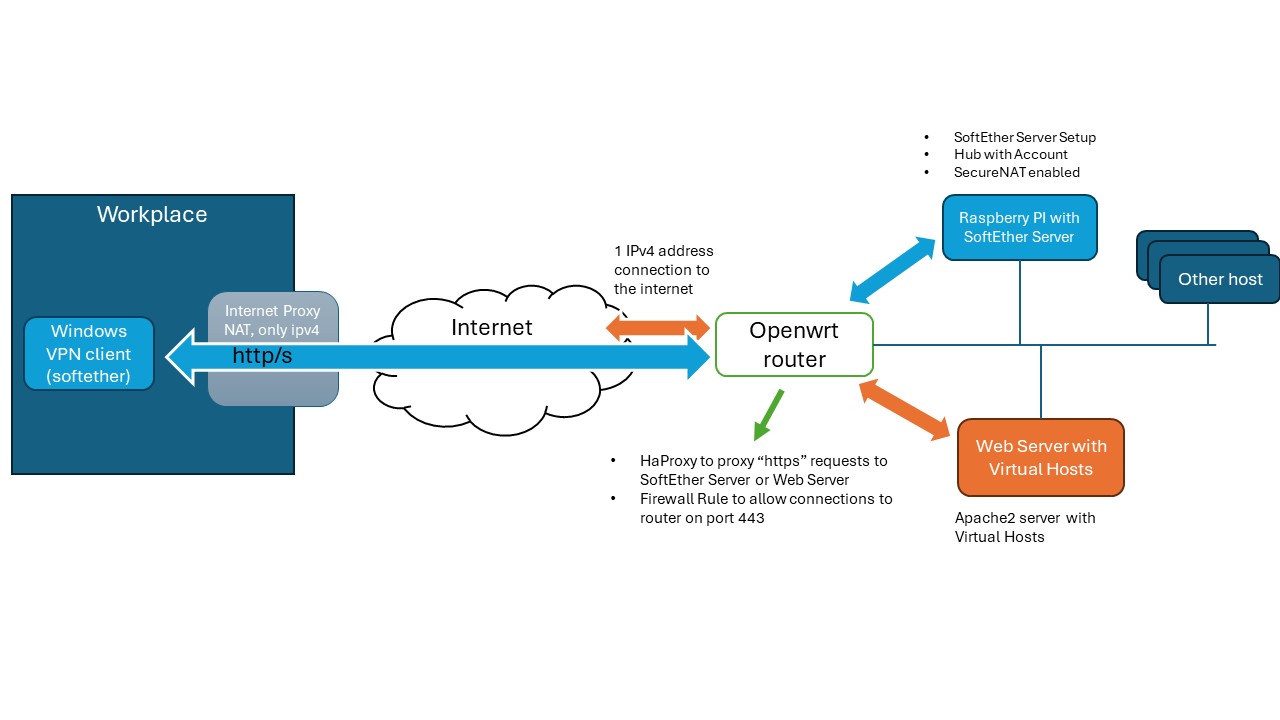
My situation is as follows:
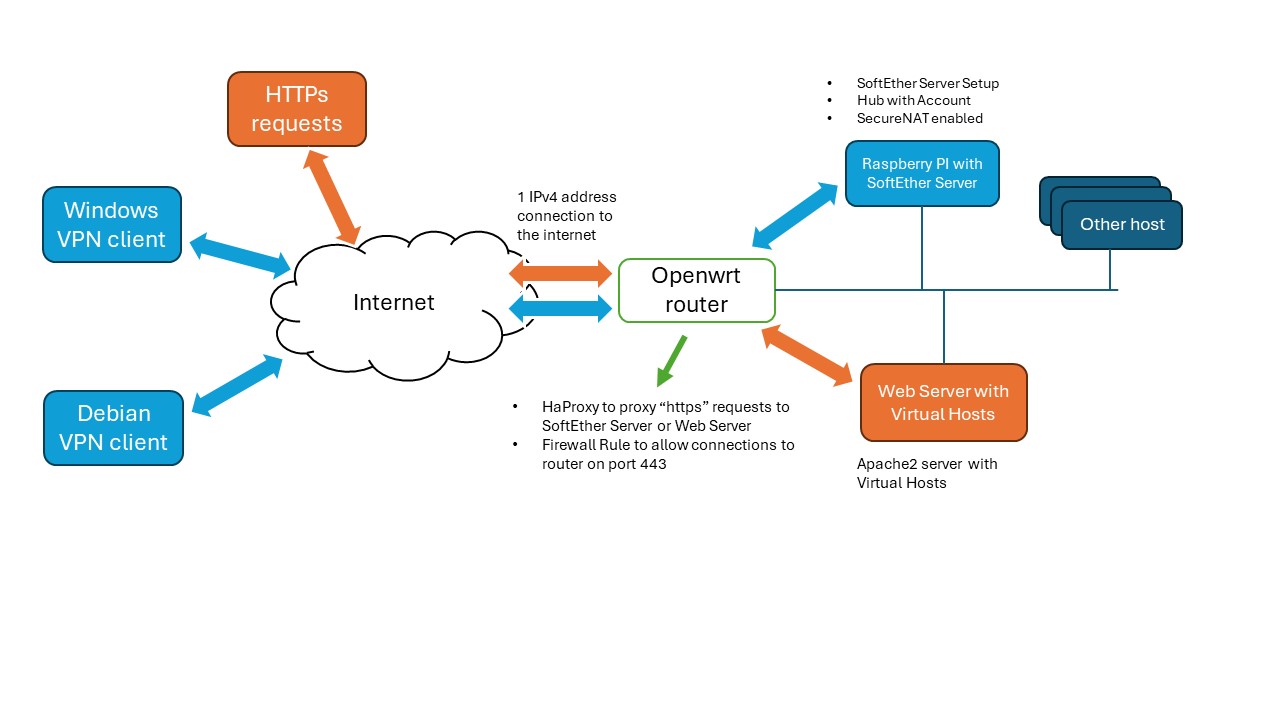
So I installed a SoftEther server on a Raspberry PI (3B+) in my internal network, which "lives" behind a router to the internet.
The router is OpenWrt based and is connected to the internet via one IPv4 address (and an ipv6 range, but that is less relevant).
I'm hosting a couple of websites on a different server.
The websites can be reached from the internet on port 80 and port 443.
I started with a simple port-forwarding rule in openwrt to forward all requests on port 80 and port 443 to the internal web server.
However, I wanted to connect to my internal home network via this VPN from my workplace, to be able to access internal files.
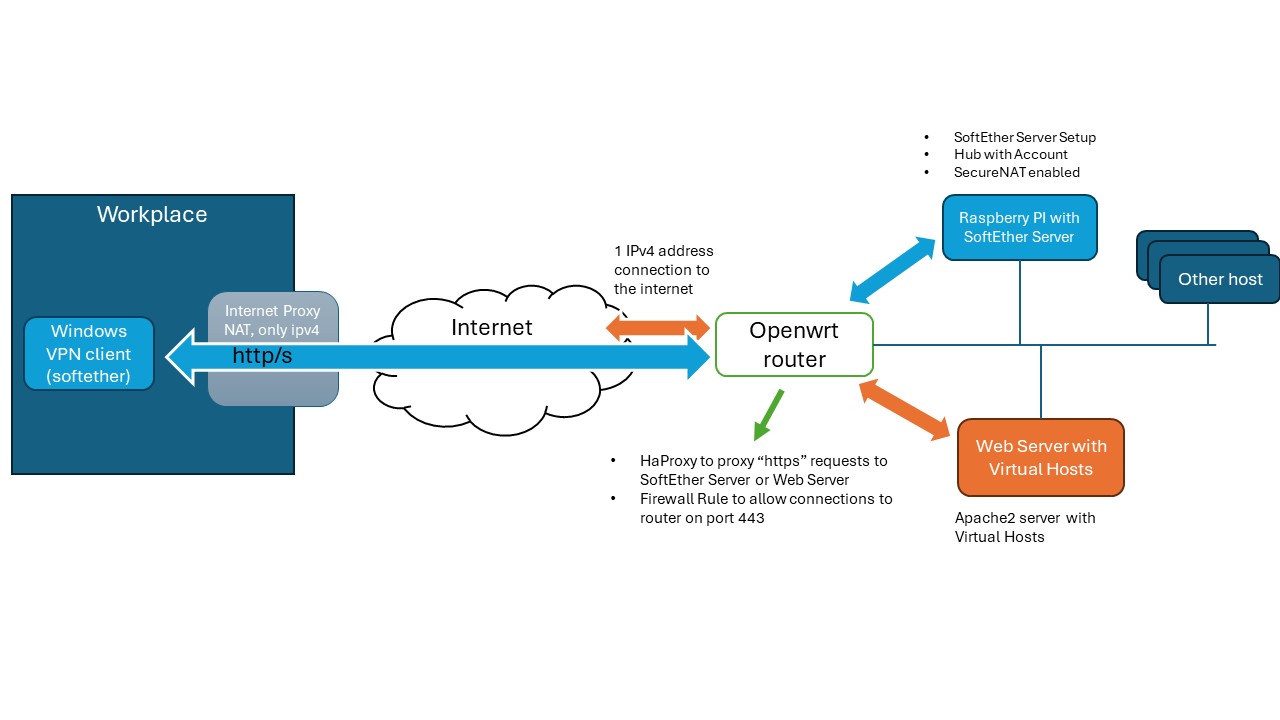
So I needed a setup over port 443 (http/s), which is what can be done with SoftEther.
It works almost out of the box with the debian installer.
Because my network is not directly connected to the internet, it will give a problem on the network part, but because of the proxy it will work.
So what to do? I want to route the VPN connection based on host name, using the same IP address to the internet.
A kind of 'virtual host', but not for http/s traffic.
Use HaProxy
* Creating a reverse proxy with Apache2 to the SoftEther Server didn't work.
* Using a simple HaProxy configuration on my openwrt router does.
What I did:
* Disabled the port forwarding rule from the internet on port 443 to the internal web server.
* Added a firewall rule to allow internet traffic on port 443 to the openwrt device.
* Installed the openwrt haproxy package, installed the rsyslog package too.
* Configured haproxy (/etc/haproxy.cfg):
Thanks to Erik Fong for his great page.
This setup works from within my workplace.
SecureNAT
I configured the server to use SecureNAT, which will also setup a dhcp server.
Works almost without configuration. It is probably a good idea to also add some routing rules.
On my debian client on the internet, I installed the softether client package.
After connecting to the configured HUB/Account over the configured virtual device (se_pk) (using vpncmd),
I had to execute dhclient vpn_se_pk to get an IP address.
Static routes
To be able to add a static route to my internal network (in this example: 10.10.10.x, but I also have a subnet 10.10.11.x), I had to manually change the configuration file and add static routes. It turns out that to add multiple lines, one has to be very precise:
Don't forget the $20 for spaces. This cannot be set from within the vpncmd CLI, so I edited the configuration file externally:
Default route on Windows
In order to not make the VPN network be the default route for all your internet traffic, it is necessary to set a metric higher than the default (1) on the VPN virtual network adapter (e.g. 300). See below:
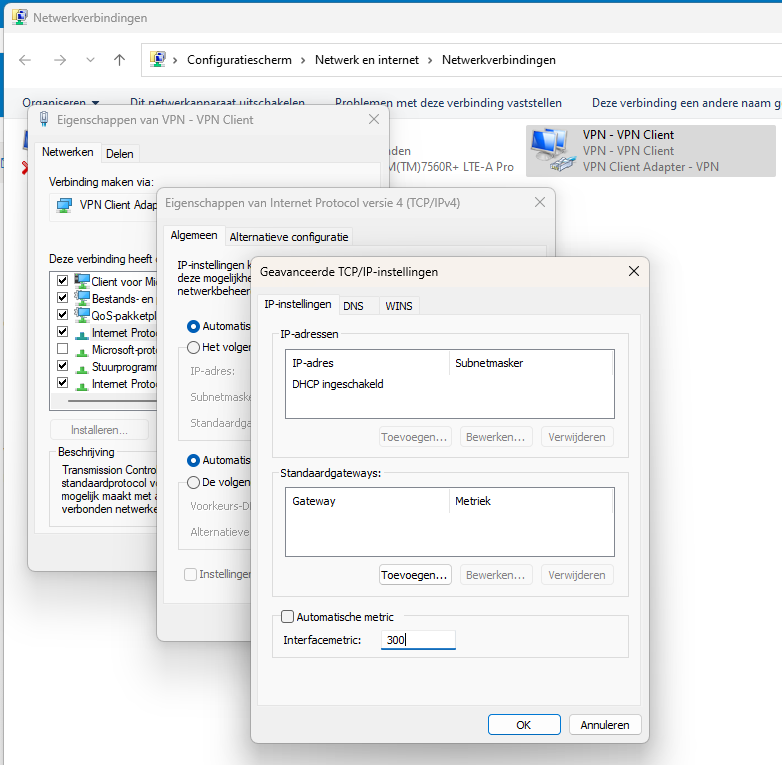
There's a drawback on windows. Although the domain name can be set on the dchp connection and the DNS server can be set for the given domain, it won't be used when the VPN adapter comes up and the metric is higher than the default. All DNS requests will go to the main DNS server (not the VPN's one). And that stops the resolving of VPN internal addresses.
This can be resolved as follows. Issue:
in powershell, which needs to be running with administrator rights, to be able to make DNS request for my internal domain to the right DNS server.
Note that nslookup will not use these rules. if you want to test the rules, it can be done either with ping or tracert.
Also note the dot (".") before the local domain. This tells Windows to resolve all subdomains of the local domain via the given nameserver(s).
Would have been nice if SoftEther would have done this out of the box.
SoftEther VPN and HTTP/s on the same IPv4 address
It is not clear right away how to setup a SoftEther VPN over port 443 shared with a HTTPs server.
My situation is as follows:
So I installed a SoftEther server on a Raspberry PI (3B+) in my internal network, which "lives" behind a router to the internet.
The router is OpenWrt based and is connected to the internet via one IPv4 address (and an ipv6 range, but that is less relevant).
I'm hosting a couple of websites on a different server.
The websites can be reached from the internet on port 80 and port 443.
I started with a simple port-forwarding rule in openwrt to forward all requests on port 80 and port 443 to the internal web server.
However, I wanted to connect to my internal home network via this VPN from my workplace, to be able to access internal files.
So I needed a setup over port 443 (http/s), which is what can be done with SoftEther.
It works almost out of the box with the debian installer.
Because my network is not directly connected to the internet, it will give a problem on the network part, but because of the proxy it will work.
Code: Select all
VPN Server>check
Check command - Check whether SoftEther VPN Operation is Possible
---------------------------------------------------
SoftEther VPN Operation Environment Check Tool
Developer Edition
Copyright (c) SoftEther VPN Project.
All Rights Reserved.
If this operation environment check tool is run on a system and that system passes, it is most likely that SoftEther VPN software can operate on that system. This check may take a while. Please wait...
(...)
Checking 'Network system'...
Connect Failed. (0)
Fail
Some checks failed. Please check the operation environment of this system. If SoftEther VPN Server / Bridge were to be executed on this system, troubles may occur.
(...)
A kind of 'virtual host', but not for http/s traffic.
Use HaProxy
* Creating a reverse proxy with Apache2 to the SoftEther Server didn't work.
* Using a simple HaProxy configuration on my openwrt router does.
What I did:
* Disabled the port forwarding rule from the internet on port 443 to the internal web server.
* Added a firewall rule to allow internet traffic on port 443 to the openwrt device.
* Installed the openwrt haproxy package, installed the rsyslog package too.
* Configured haproxy (/etc/haproxy.cfg):
Code: Select all
global
# log to rsyslog (this is optional)
log 127.0.0.1:514 local1
# daemonize haproxy
daemon
defaults
# set some defaults
timeout client 30s
timeout server 30s
timeout connect 5s
frontend ft_tcp
# bind on port 443
mode tcp
bind *:443
# Delay required so there's time to get the required information
tcp-request inspect-delay 5s
# Inspect the SSL "hello" to get the required hostname
tcp-request content accept if { req_ssl_hello_type 1 }
# Redirect traffic to the softether server if the host matches
use_backend bk_softether if { req_ssl_sni -i vpn.mydomain.nl }
#Otherwise use the normal https backend
default_backend bk_tcp_to_https
backend bk_softether
mode tcp
server server-se 10.10.10.200:443
backend bk_tcp_to_https
mode tcp
server haproxy-https 10.10.10.100:443
This setup works from within my workplace.
SecureNAT
I configured the server to use SecureNAT, which will also setup a dhcp server.
Works almost without configuration. It is probably a good idea to also add some routing rules.
On my debian client on the internet, I installed the softether client package.
After connecting to the configured HUB/Account over the configured virtual device (se_pk) (using vpncmd),
I had to execute dhclient vpn_se_pk to get an IP address.
Static routes
To be able to add a static route to my internal network (in this example: 10.10.10.x, but I also have a subnet 10.10.11.x), I had to manually change the configuration file and add static routes. It turns out that to add multiple lines, one has to be very precise:
Code: Select all
string DhcpPushRoutes 10.10.2.0/255.255.255.0/192.168.30.1,$2010.10.3.0/255.255.255.0/192.168.30.1,$20192.168.137.0/255.255.255.0/192.168.30.1
Code: Select all
root@host:/var/lib/softether# service softether-vpnserver stop
vi vpn_server.config
(.., look for DhcpPush, change $ into 10.10.2.0/255.255.0.0/192.168.30.1,$2010.10. etc.)
root@host:/var/lib/softether# service softether-vpnserver start
In order to not make the VPN network be the default route for all your internet traffic, it is necessary to set a metric higher than the default (1) on the VPN virtual network adapter (e.g. 300). See below:
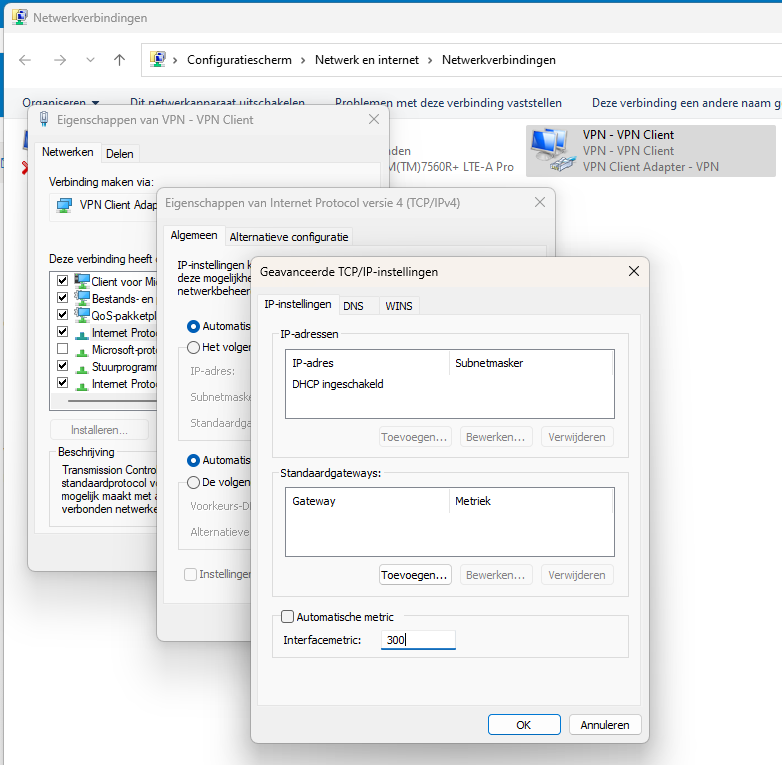
There's a drawback on windows. Although the domain name can be set on the dchp connection and the DNS server can be set for the given domain, it won't be used when the VPN adapter comes up and the metric is higher than the default. All DNS requests will go to the main DNS server (not the VPN's one). And that stops the resolving of VPN internal addresses.
This can be resolved as follows. Issue:
Code: Select all
Add-DnsClientNrptRule -Namespace ".mydomain.local" -NameServers "10.10.3.23"
Add-DnsClientNrptRule -Namespace ".myotherdomain.local" -NameServers "10.10.3.23"
Note that nslookup will not use these rules. if you want to test the rules, it can be done either with ping or tracert.
Also note the dot (".") before the local domain. This tells Windows to resolve all subdomains of the local domain via the given nameserver(s).
Would have been nice if SoftEther would have done this out of the box.
